The first stable release of the new year has been released today, version 24. The Chrome team boasts speed and security improvements.
The main new feature to Chrome 24 is support for MathML, which is XML markup for adding mathematical equations into webpages. There is now support for HTML 5 datalists for date and time, which allows you to specify a list of suggested dates and times for input elements within webpages.
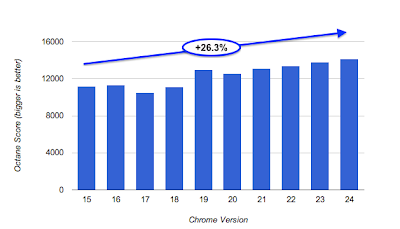
Chrome 24 features improving browsing speed and Cloud Print now operates faster. Over the past 12 months, Chrome has become 26% faster!
Chrome 24 also features a slue of security updates, making your browsing experience even more secure!
- [162494] High CVE-2012-5145: Use-after-free in SVG layout. Credit to Atte Kettunen of OUSPG.
- [165622] High CVE-2012-5146: Same origin policy bypass with malformed URL. Credit to Erling A Ellingsen and Subodh Iyenger, both of Facebook.
- [165864] High CVE-2012-5147: Use-after-free in DOM handling. Credit to José A. Vázquez.
- [167122] Medium CVE-2012-5148: Missing filename sanitization in hyphenation support. Credit to Google Chrome Security Team (Justin Schuh).
- [166795] High CVE-2012-5149: Integer overflow in audio IPC handling. Credit to Google Chrome Security Team (Chris Evans).
- [165601] High CVE-2012-5150: Use-after-free when seeking video. Credit to Google Chrome Security Team (Inferno).
- [165538] High CVE-2012-5151: Integer overflow in PDF JavaScript. Credit to Mateusz Jurczyk, with contribution from Gynvael Coldwind, both of Google Security Team.
- [165430] Medium CVE-2012-5152: Out-of-bounds read when seeking video. Credit to Google Chrome Security Team (Inferno).
- [164565] High CVE-2012-5153: Out-of-bounds stack access in v8. Credit to Andreas Rossberg of the Chromium development community.
- [Windows only] [164490] Low CVE-2012-5154: Integer overflow in shared memory allocation. Credit to Google Chrome Security Team (Chris Evans).
- [Mac only] [163208] Medium CVE-2012-5155: Missing Mac sandbox for worker processes. Credit to Google Chrome Security Team (Julien Tinnes).
- [162778] High CVE-2012-5156: Use-after-free in PDF fields. Credit to Mateusz Jurczyk, with contribution from Gynvael Coldwind, both of Google Security Team.
- [162776] [162156] Medium CVE-2012-5157: Out-of-bounds reads in PDF image handling. Credit to Mateusz Jurczyk, with contribution from Gynvael Coldwind, both of Google Security Team.
- [162153] High CVE-2013-0828: Bad cast in PDF root handling. Credit to Mateusz Jurczyk, with contribution from Gynvael Coldwind, both of Google Security Team.
- [162114] High CVE-2013-0829: Corruption of database metadata leading to incorrect file access. Credit to Google Chrome Security Team (Jüri Aedla).
- [Windows only] [162066] Low CVE-2013-0830: Missing NUL termination in IPC. Credit to Google Chrome Security Team (Justin Schuh).
- [161836] Low CVE-2013-0831: Possible path traversal from extension process. Credit to Google Chrome Security Team (Tom Sepez).
- [160380] Medium CVE-2013-0832: Use-after-free with printing. Credit to Google Chrome Security Team (Cris Neckar).
- [154485] Medium CVE-2013-0833: Out-of-bounds read with printing. Credit to Google Chrome Security Team (Cris Neckar).
- [154283] Medium CVE-2013-0834: Out-of-bounds read with glyph handling. Credit to Google Chrome Security Team (Cris Neckar).
- [152921] Low CVE-2013-0835: Browser crash with geolocation. Credit to Arthur Gerkis.
- [150545] High CVE-2013-0836: Crash in v8 garbage collection. Credit to Google Chrome Security Team (Cris Neckar).
- [145363] Medium CVE-2013-0837: Crash in extension tab handling. Credit to Tom Nielsen.
- [Linux only] [143859] Low CVE-2013-0838: Tighten permissions on shared memory segments. Credit to Google Chrome Security Team (Chris Palmer).
Finally, Webkit has been updated to version 537.17 and V8 has been updated to version 3.14.5.0
